MIL-OSI Security: Principal Deputy Assistant Attorney General David Newman Delivers Remarks at 2024 U.S. Cyber Command Legal Conference
It deserves emphasizing that this is a team sport: Even as the operations relied on Justice Department legal process, we are often not alone in planning or executing them. We are almost always joined by a coalition of U.S. government, private sector, and foreign partners in this work.
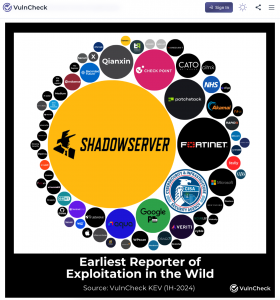
In disrupting the GRU botnet, for example, we planned and coordinated with the Shadowserver Foundation, Microsoft, and other private sector partners. Shortly after we announced the operation, the FBI, NSA, Cyber Command, and 11 foreign partner entities released a joint cybersecurity advisory providing device owners and network defenders with valuable threat intelligence about the GRU’s relevant tactics, techniques, and procedures. Many of these same partners provided invaluable assistance in eradicating portions of the botnet within their borders.